I love the idea of Pixelfed and briefly checked it out a couple years ago, bounced off it b/c hash tags weren’t federated, and other issues that I don’t remember the specifics of. For example, when I click on #cats in a photo caption, I want it to show me photos across all instances w/ that hash tag, like the “All” feed in Lemmy.
I don’t wanna poo poo on something that is essentially a free service for plebs like myself, but I remember things being just broken/ incomplete enough and it seemed like its original creator had already moved on to other projects that I filed it under “things w/ potential that aren’t quite there yet (and may never get there).”







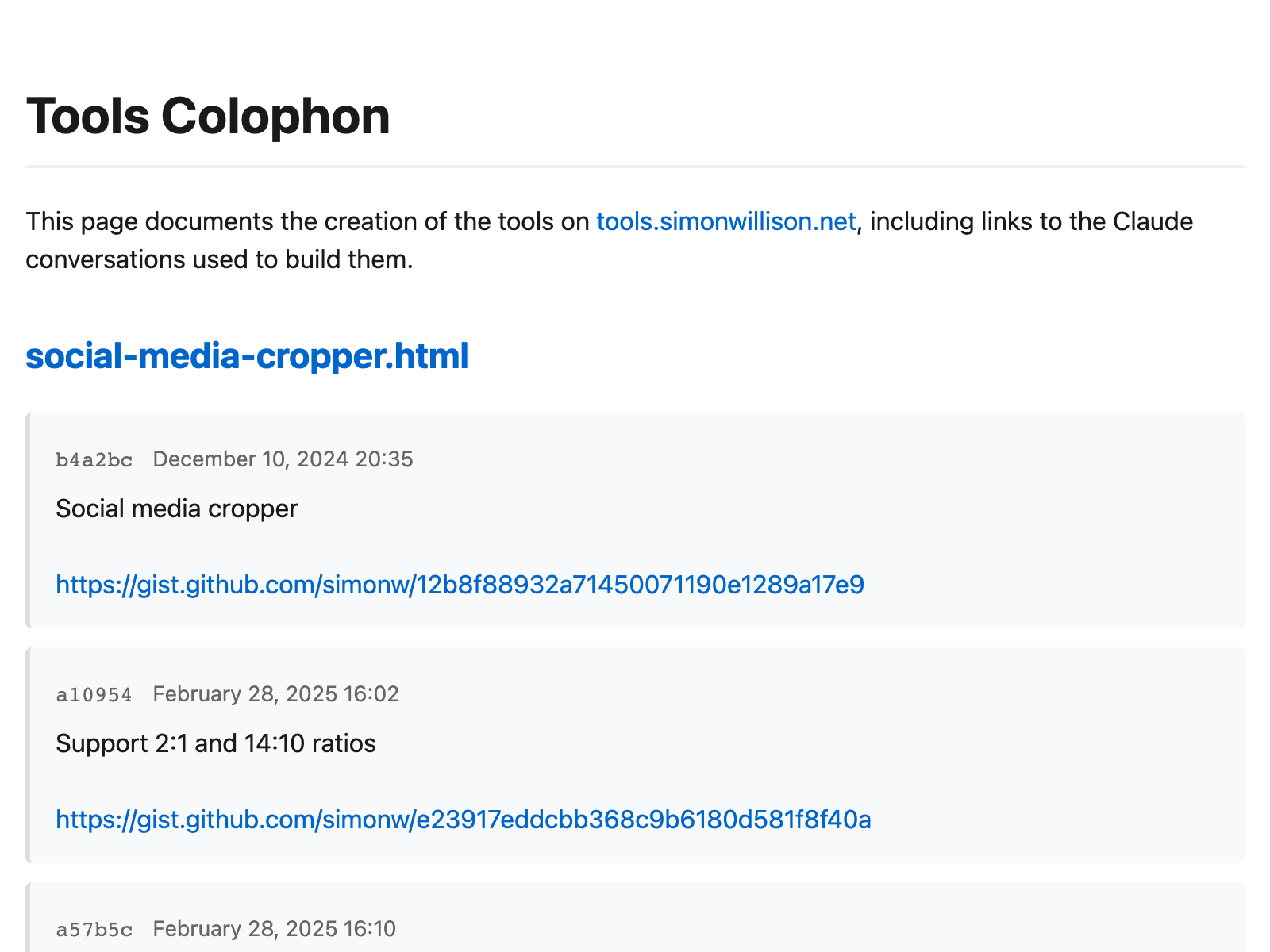

From their GH: